LDAP + local users
Use centralized identity with LDAP while preserving local accounts for platform administration and break-glass access.
DBAegis is positioned for enterprise buyers who need access discipline, encrypted secrets, restore authorization, and audit-ready recovery workflows in a self-hosted platform.
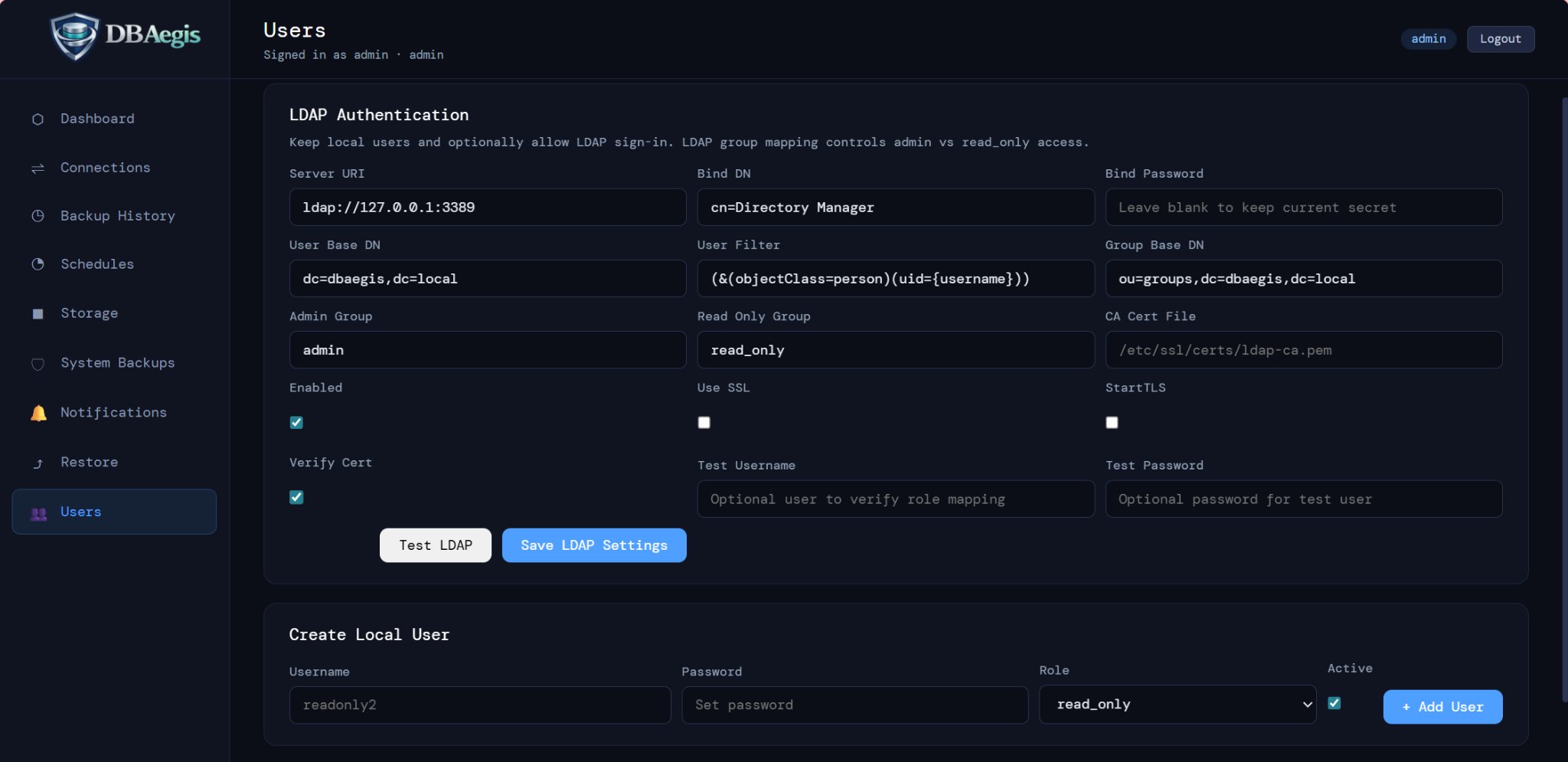
Use centralized identity with LDAP while preserving local accounts for platform administration and break-glass access.
Role-based access control separates admin and read-only responsibilities and supports group mapping for cleaner governance.
Enable TLS for the tool and secure LDAP with SSL/StartTLS and certificate verification where required.
Connection passwords and sensitive credentials are stored encrypted, with secret-key rotation called out as a security practice.
Webhook integrations should be validated, restricted, and monitored so notification endpoints do not weaken platform posture.
Password re-authorization, restore reason capture, dry runs, and typed confirmation help prevent accidental or unauthorized restores.
Capture who initiated restore, which artifact was used, what target was selected, when the action occurred, and why the restore was needed.
System snapshots protect DBAegis metadata and configuration so the control plane itself can be recovered after server or deployment issues.
The PHP chat proxy files now allow only configured DBAegis origins instead of returning Access-Control-Allow-Origin: *. Update the allowed origin list if you use staging domains.